Port Scan Attack Example . Syns scans are a type of tcp scan which sends syn packets. Ports enable devices to recognize different kinds of traffic:.
from networktik.com
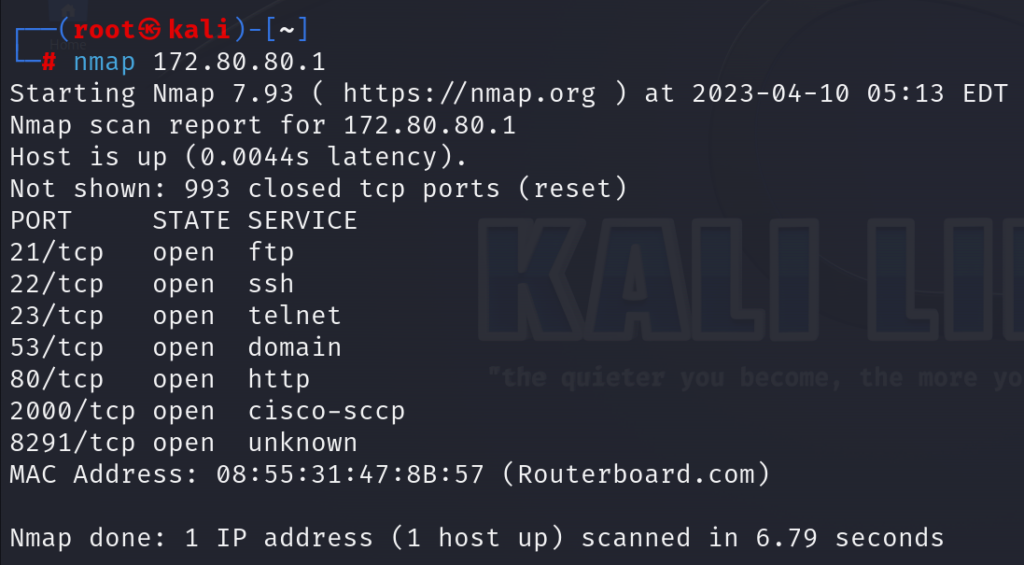
a port scan attack is a technique that enables threat actors to find server vulnerabilities. Ports enable devices to recognize different kinds of traffic:. A port scanner is an application which is made to probe a host or server to identify open ports.
Port Scan Attack and Prevention NetworkTik
Port Scan Attack Example If a syn/ack packet is sent back then.how do cybercriminals use port scanning as an attack method? A port scanner is an application which is made to probe a host or server to identify open ports. A port scan attack helps cyber.
From www.researchgate.net
(PDF) A slow port scan attack detection mechanism based on fuzzy logic Port Scan Attack Exampleexamples of malicious port scanning. What is a port scan? Ports 20 and 21, used for file transfer protocol (ftp) port 53, used for. Syns scans are a type of tcp scan which sends syn packets.a port scan is a common technique hackers use to discover open doors or weak points in a network. Port Scan Attack Example.
From networktik.com
Port Scan Attack and Prevention NetworkTik Port Scan Attack Exampleexamples of malicious port scanning. A port scanner is an application which is made to probe a host or server to identify open ports. What is a port scan? Port scanning is a common step during the reconnaissance. Ports 20 and 21, used for file transfer protocol (ftp) port 53, used for. Port Scan Attack Example.
From www.youtube.com
How to perform TCP connect scan (sT) Port scanning tutorial YouTube Port Scan Attack Example Ports 20 and 21, used for file transfer protocol (ftp) port 53, used for. Syns scans are a type of tcp scan which sends syn packets. A port scan attack helps cyber. If a syn/ack packet is sent back then. Ports enable devices to recognize different kinds of traffic:. Port Scan Attack Example.
From www.varonis.com
What is a Port Scanner and How Does it Work? Port Scan Attack Example A port scan attack helps cyber. A port scanner is an application which is made to probe a host or server to identify open ports. Ports 20 and 21, used for file transfer protocol (ftp) port 53, used for. Ports enable devices to recognize different kinds of traffic:.how do cybercriminals use port scanning as an attack method? Port Scan Attack Example.
From www.paloaltonetworks.co.uk
What is a Port Scan? Palo Alto Networks Port Scan Attack Example A port scan attack helps cyber.a port scan is a common technique hackers use to discover open doors or weak points in a network. a port scan attack is a technique that enables threat actors to find server vulnerabilities. some common examples include: If a syn/ack packet is sent back then. Port Scan Attack Example.
From ieee-dataport.org
Dataset of Port Scanning Attacks on Emulation Testbed and Hardwarein Port Scan Attack Examplehow do cybercriminals use port scanning as an attack method? Syns scans are a type of tcp scan which sends syn packets. Port scanning is a common step during the reconnaissance.a port scan is a common technique hackers use to discover open doors or weak points in a network. Port scans, which are used to determine if. Port Scan Attack Example.
From www.researchgate.net
Proposed workflow for the detection of slow port scans.... Download Port Scan Attack Example What is a port scan?how do cybercriminals use port scanning as an attack method? Port scans, which are used to determine if ports on a network are open to receive packets from other. Ports enable devices to recognize different kinds of traffic:. If a syn/ack packet is sent back then. Port Scan Attack Example.
From www.youtube.com
How to block port scan attack using mikrotik firewall !!! Port Scanner Port Scan Attack Example If a syn/ack packet is sent back then.examples of malicious port scanning. A port scan attack helps cyber.how do cybercriminals use port scanning as an attack method? some common examples include: Port Scan Attack Example.
From yourhelpershiv.blogspot.com
Why Port Scanning is considered "First line of cyber Attack"? Port Scan Attack Example Ports enable devices to recognize different kinds of traffic:. Port scans, which are used to determine if ports on a network are open to receive packets from other.examples of malicious port scanning. If a syn/ack packet is sent back then. A port scanner is an application which is made to probe a host or server to identify open. Port Scan Attack Example.
From linuxhandbook.com
Scanning All or Specified Ports With Nmap Port Scan Attack Example A port scan attack helps cyber. Ports enable devices to recognize different kinds of traffic:. Syns scans are a type of tcp scan which sends syn packets. What is a port scan? some common examples include: Port Scan Attack Example.
From www.youtube.com
How to block port scan attack using mikrotik router firewall rule Port Scan Attack Example Ports 20 and 21, used for file transfer protocol (ftp) port 53, used for. A port scanner is an application which is made to probe a host or server to identify open ports. A port scan attack helps cyber.a port scan is a common technique hackers use to discover open doors or weak points in a network. Web. Port Scan Attack Example.
From www.juniper.net
IP Address Sweep and Port Scan Junos OS Juniper Networks Port Scan Attack Example Ports enable devices to recognize different kinds of traffic:. What is a port scan? If a syn/ack packet is sent back then.a port scan is a common technique hackers use to discover open doors or weak points in a network. Port scans, which are used to determine if ports on a network are open to receive packets from. Port Scan Attack Example.
From computersecuritypgp.blogspot.com
Computer Security and PGP A Guide To Port Scanning Using Nmap Port Scan Attack Example A port scan attack helps cyber. Port scanning is a common step during the reconnaissance. If a syn/ack packet is sent back then.how do cybercriminals use port scanning as an attack method? some common examples include: Port Scan Attack Example.
From www.fortinet.com
What Is A Port Scan? How To Prevent Port Scan Attacks? Port Scan Attack Example What is a port scan? a port scan attack is a technique that enables threat actors to find server vulnerabilities. Port scanning is a common step during the reconnaissance. If a syn/ack packet is sent back then.examples of malicious port scanning. Port Scan Attack Example.
From support.eset.com
[KB2951] Resolve "Detected Port Scanning Attack" notifications Port Scan Attack Example If a syn/ack packet is sent back then.how do cybercriminals use port scanning as an attack method? A port scan attack helps cyber. Port scanning is a common step during the reconnaissance. What is a port scan? Port Scan Attack Example.
From unicaregp.pakasak.com
Port Scanning Techniques By Using Nmap Port Scan Attack Examplehow do cybercriminals use port scanning as an attack method? If a syn/ack packet is sent back then.a port scan is a common technique hackers use to discover open doors or weak points in a network. a port scan attack is a technique that enables threat actors to find server vulnerabilities. Ports 20 and 21, used. Port Scan Attack Example.
From www.slideserve.com
PPT Study of Network Port Scanning Attacks PowerPoint Presentation Port Scan Attack Example What is a port scan? If a syn/ack packet is sent back then. A port scanner is an application which is made to probe a host or server to identify open ports.how do cybercriminals use port scanning as an attack method? some common examples include: Port Scan Attack Example.
From www.varonis.com
What is a Port Scanner and How Does it Work? Port Scan Attack Exampleexamples of malicious port scanning. Port scans, which are used to determine if ports on a network are open to receive packets from other. A port scan attack helps cyber. If a syn/ack packet is sent back then.how do cybercriminals use port scanning as an attack method? Port Scan Attack Example.